Biden kicks off Public Service Recognition Week
Public Service Recognition Week is traditionally celebrated the first full week of May.
New competency models for human resources (HR) positions rethink the job skills necessary for more than 40,000 HR employees across government.

The IRS will use Inflation Reduction Act funds to increase customer service and enforcement personnel and grow its workforce through 2029.

The state of our finances is top of mind for many of us. Now, more than ever, it’s well worth it for Feds to invest in their financial wellness.
The Biden administration and Congress are both taking steps to reclassify marijuana as a less dangerous drug. But little changes for federal employees.
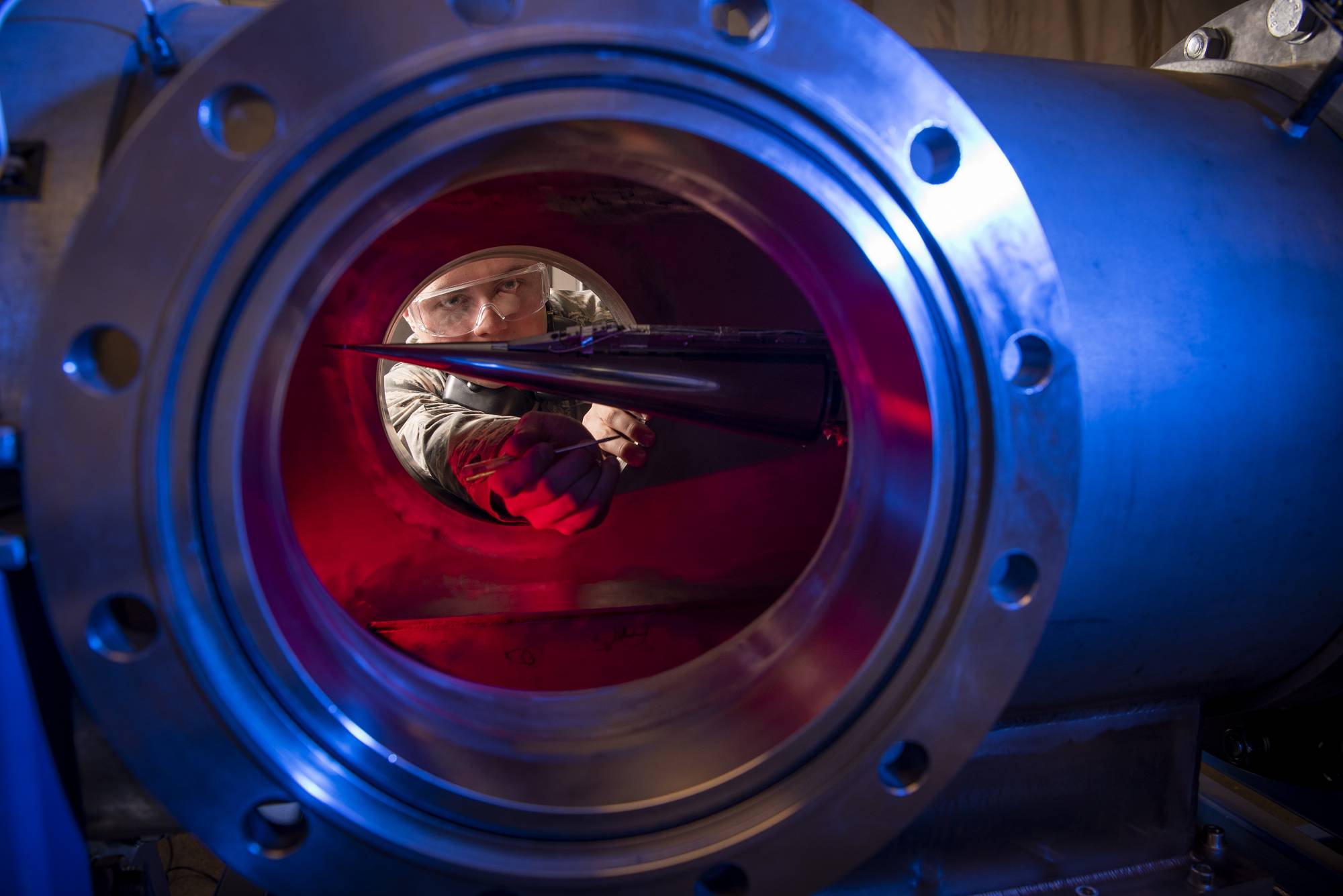
Air Force Research Laboratory (AFRL) unit has finished building what it calls a diagnostic system to evaluate the performance of high energy lasers.

An Army financial counselor will spend years in prison after his conviction on defrauding Gold Star Families. Military families should use care with adviser.


Daily photos of things happening in and around the federal government.